CASE STUDY
Implementation of eAuditor
at the District Court
Find out how the implementation at the judicial institution looked like.
What kind of system was the client looking for?
The client was looking for a solution that could provide them with a high level of data security, as well as effective management of IT infrastructure in a multi-branch structure such as the courts. The eAuditor system, due to its innovative features, met the client’s expectations. The ability to ensure data security through built-in remote disk encryption mechanisms, prevailed in choosing our system. The client wanted a system that would allow:
What was the implementation of the eAuditor system like?
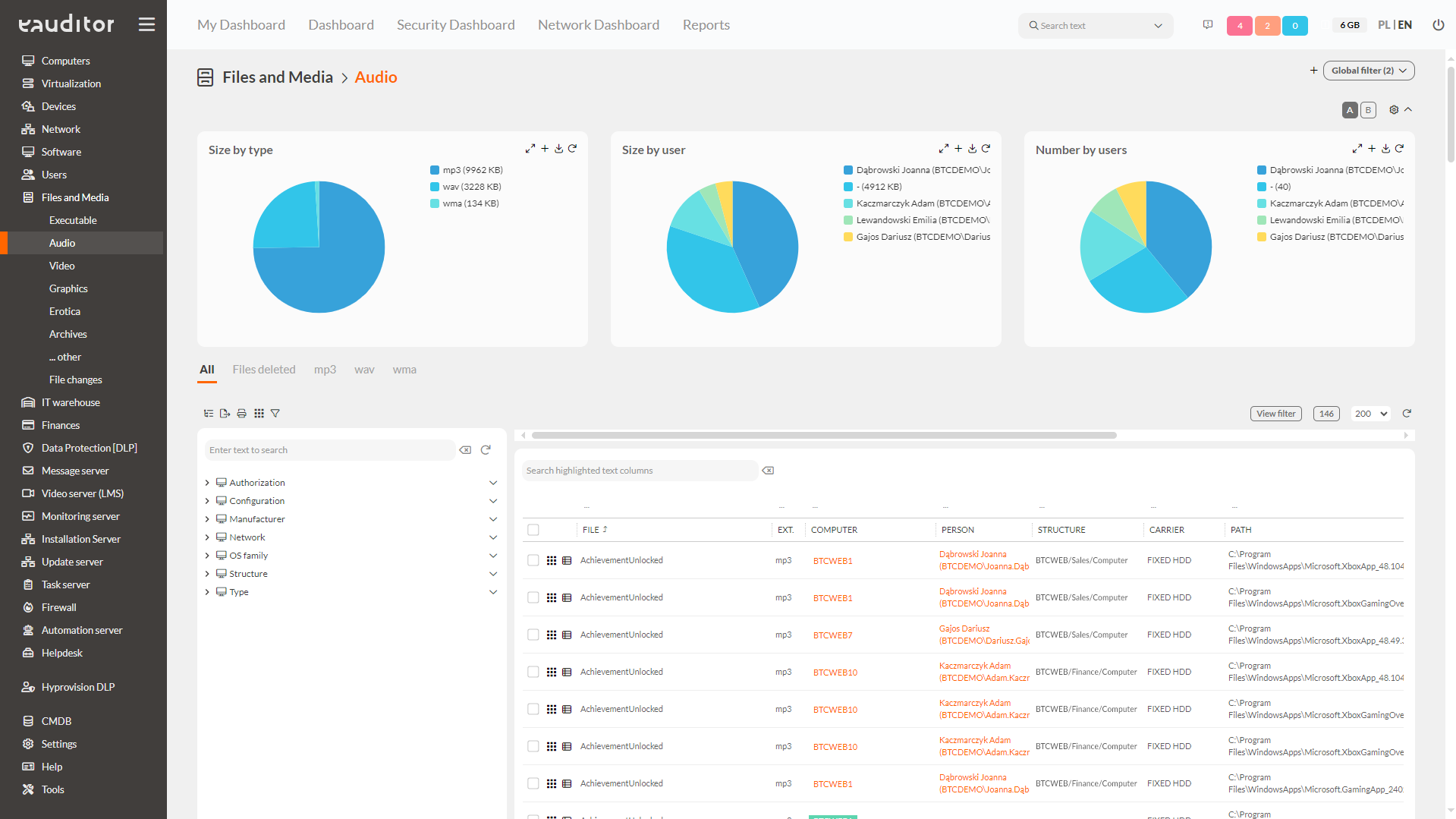
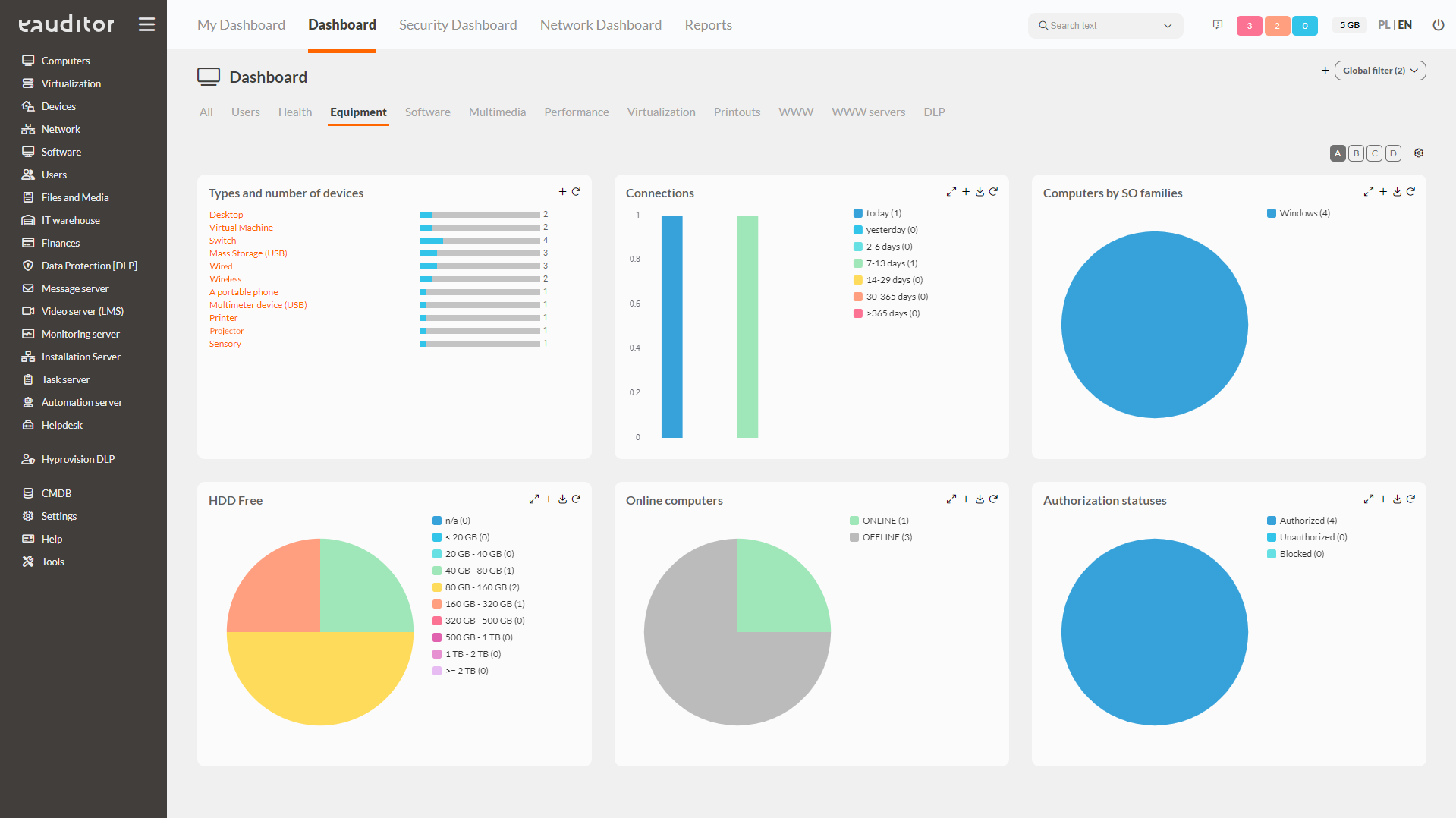
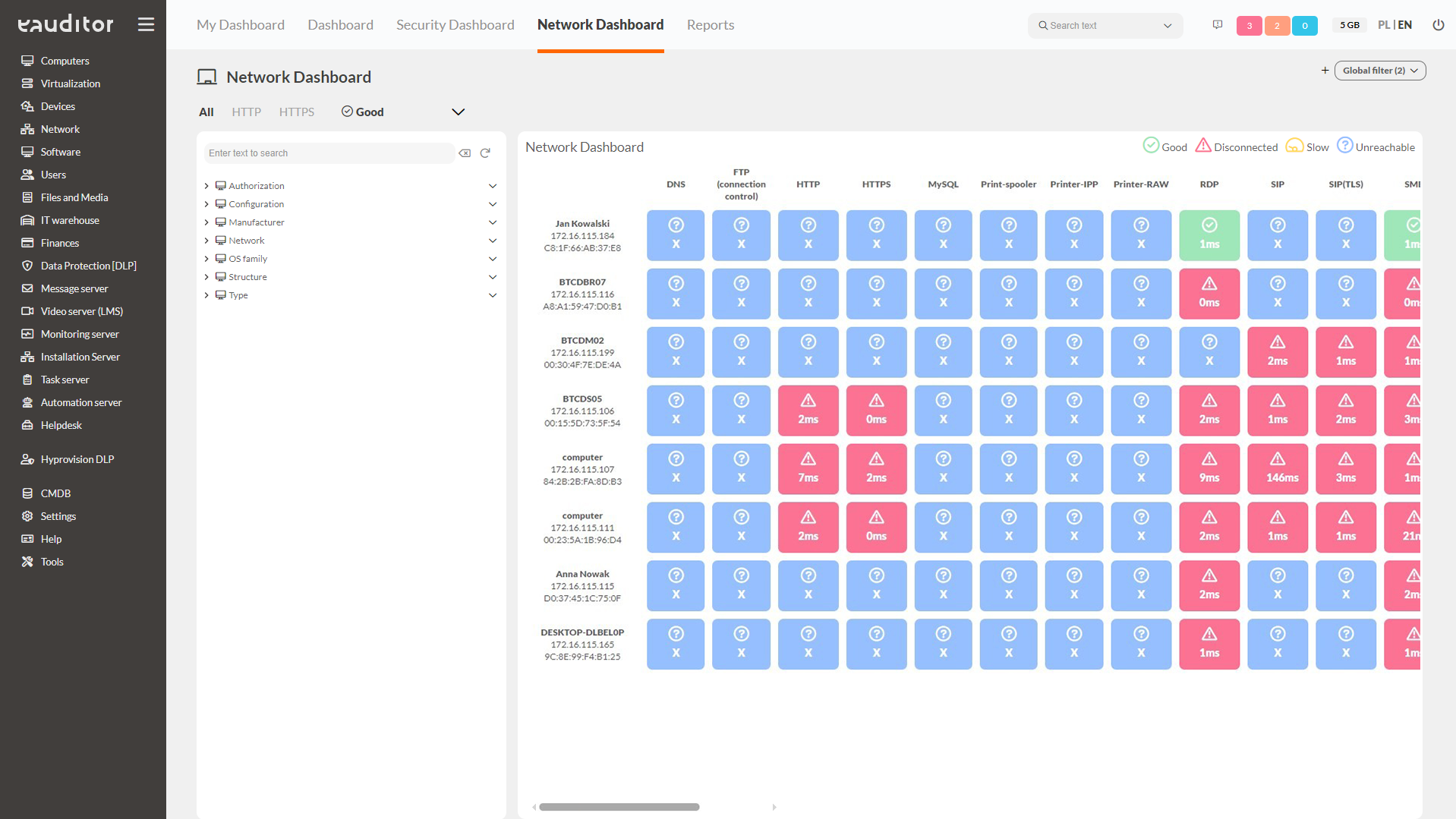
The implementation process took place with full support in the configuration and profiling of the system. We also provided training to ensure the most optimal use of the system. The customer opted for a network scanner to image the connections between all devices. In addition, the client expanded the basic version of the system to include a scheduling and report creation function, which gave it the ability to modify built-in reports, as well as create its own. Advanced and predefined reports have certainly improved work efficiency. Due to the nature of an institution such as a court, the client also opted for the ability to remotely encrypt disks using the BitLocker method.In summary, the client opted for additional functionality such as:
What did the customer gain?
The eAuditor system, due to its comprehensiveness, as well as the intuitiveness and efficiency of the solution, has proven itself perfectly in an institution such as a court. After 2 years of use, the client decided to expand the license and purchase an additional 60 devices for its subordinate District Court. The client’s goal was to be able to manage both areas from a single console. With eAuditor, this was possible because the system makes it possible to manage software and IT infrastructure in complex organizational structures.
The customer had two choices:
- Connect two networks via VPN and manage everything unchanged.
- Configure eAgents running on computers in the subordinate area using the so-called the alternative IP address of the communication server. Using this solution allowed the agent to communicate from outside the local network.
Both solutions provided the client with a fully encrypted connection. By setting up eAgents, the client was able to manage the IT infrastructure of both courts from a single web-based console.
In addition, the eAuditor System, thanks to its automatic inventory of computers and servers, as well as its ability to monitor connections between devices on the network, has significantly contributed to improving the efficiency and effectiveness of IT infrastructure management. It has streamlined and automated work, and through the ability to remotely encrypt disks, it has ensured data security. The appropriate configuration of eAgents made it possible to manage computers in a distributed infrastructure, regardless of which network the devices were on.