Blocking access to websites and running processes
- BTC Website Classification
- BTC Process Classification
- Process and Website Classification
Table of contents
Blocking access to websites and running processes
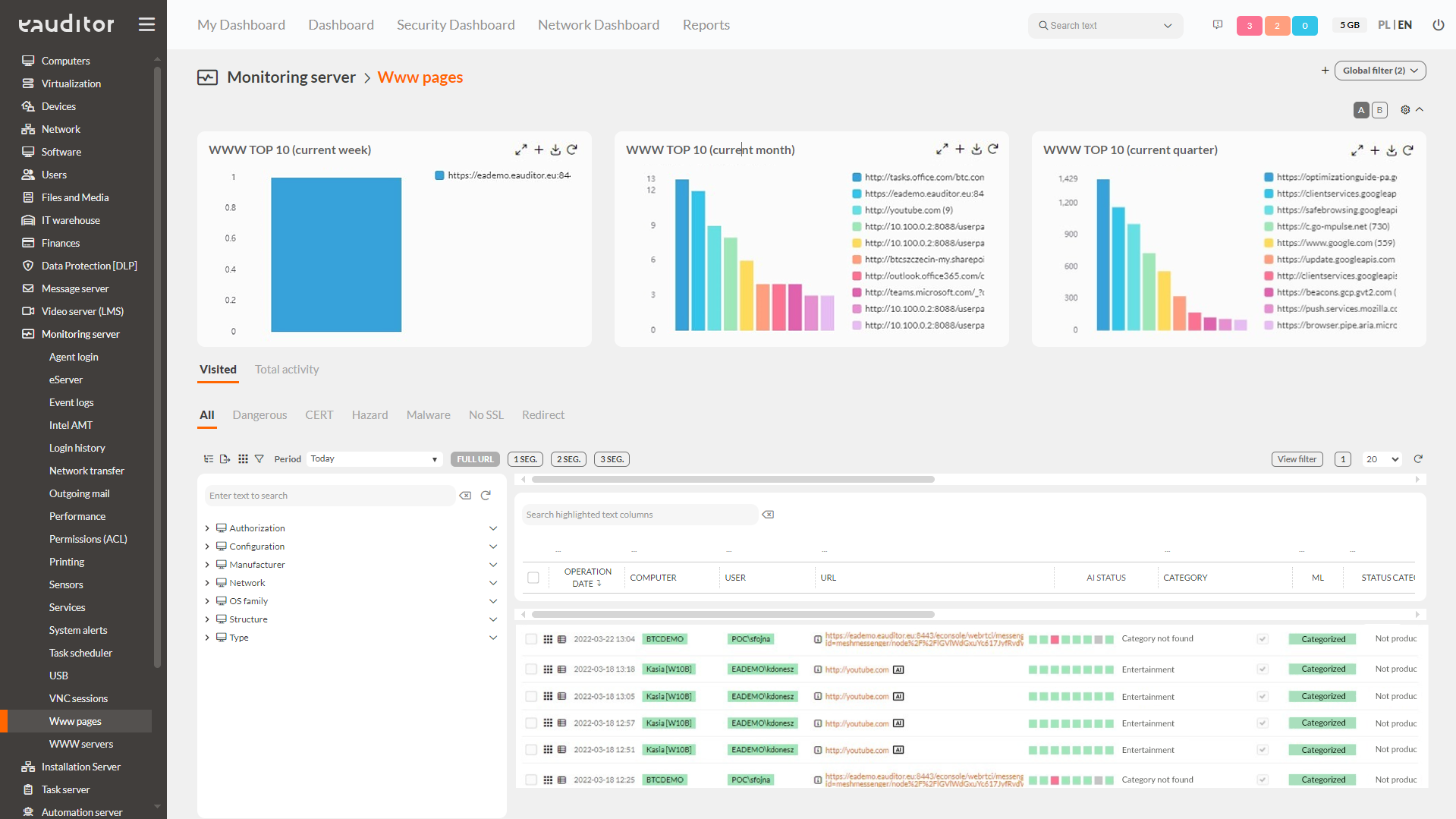
BTC Website Classification
BTC Website Classification has a real impact on IT security. The classifier analyzes URLs used by employees and checks whether their category is secure. Based on its analysis, it is enough to identify sites as having an unsafe category, an invalid SSL certificate, or being on the registry of gambling sites. The classifier analyzes Web pages to look for potential dangers. As a result, it is able to react more quickly to an impending threat and protect the organization from intentional or accidental data leaks.
Sites are analyzed from external databases such as:
- CERT databases,
- Register of Gambling Sites,
- URL Haus database.
- Websites are analyzed for:
- site language,
- web structure,
- category security information,
- category productivity information,
- SSL certificate validity,
- presence of redirects.
Details about BTC Website Classification can be found here.
Benefits
BTC Process Classification
Process and application classification has a real impact on the security of an organization. BTC Process Classification monitors and analyzes all processes and applications run by users in real time. This makes it possible to react much faster to an impending threat and protect data from attacks. BTC Classifier performs a detailed security analysis in real time. The classifier is also equipped with a number of mechanisms that automatically reject erroneous processes. In addition, its engine is located in a Data Center and is supported by a scalable set of servers, which ensures unlimited performance of the solution.
Details about BTC Process Classification can be found here.